Are VPN providers more trustworthy than your ISP?
Introduction
VPN stands for “Virtual Private Network” and creates an encrypted communication / tunnel, between your computer and the VPN Provider’s server that you connect to. When using free public Wi-Fi at a coffee shop or airport, a VPN ensures that no one around you can intercept your browsing traffic or whatever you are doing online. A VPN is also useful when you are in a country that is blocking access to certain websites, or when you are in the USA, where an internet provider is allowed to sell its customer’s browsing data.
Many articles have been published online explaining the reasons why you should use a VPN service/provider when you are connected to the internet. Some prefer to use a VPN only when connected to public Wi-Fi networks, others prefer to have a VPN activated all the time.
Looking at the privacy offered by different VPN providers, the website Torrentfreak interviewed several VPN providers about their policy rules and how they provide anonymity to the users.
Another great starting point before selecting your VPN provider is “The One Privacy Site” which has an excellent overview about the jurisdiction, logging policies and more for nearly every VPN provider on the market.
There are some known incidents you should know when it comes to privacy surrounding VPN providers.
Reported incidents with VPN providers
Recently there have been two incidents which have shocked many users in the VPN community, which at the same time were not so surprising at all.
1) The “free” VPN provider “Hotspot Shield VPN” is selling user data to advertisers.
Well it’s “free”, so what are you expecting? That’s the reason why I can’t recommend using any free VPN service available. Maintaining the VPN infrastructure costs money by either maintaining their own servers or buying access to servers on locations in different countries. If those things come for free, then it’s not surprising for me that the user is paying the price for it.
2) PureVPN logs were used by the FBI to track and arrest an internet stalker.
If you read PureVPN’s Terms of service for example, it states:
Use our Website and/or Services to harm, threaten, ’stalk’ or otherwise harass another person/business.
Additionally PureVPN write the following about account information in the Privacy Policy:
“The data that we do keep is strictly for accounting purposes, and prevent fraud now and in the future.”
Means that logging is done by VPN providers.
Logging done by VPN providers
Of course VPN providers are logging “some” data, often at least so called “connection logs”. How much they are logging differs from provider to provider. Read the Terms of use, Logging and Privacy policies of the VPN provider you want to use. Visit “The One Privacy Site” for more information about how much data each provider is logging.
Keep in mind that basically all of the VPN providers have the ability to report abuse of their service.
A VPN is exchanging your internet exit point
A VPN changes your “internet exit point” – egress point – from your local internet service provider (ISP) to the VPN server used by the VPN provider. The communication between your computer to the VPN provider’s internet exit point is encrypted. From there on, the traffic appears the same as if it is leaving your ISP at home. This means that you must also trust the outbound infrastructure from the VPN server. You need to trust the company who is maintaining the VPN servers and by this, the egress point used by the VPN provider. You also need to trust the internet provider and the country it is hosted in.
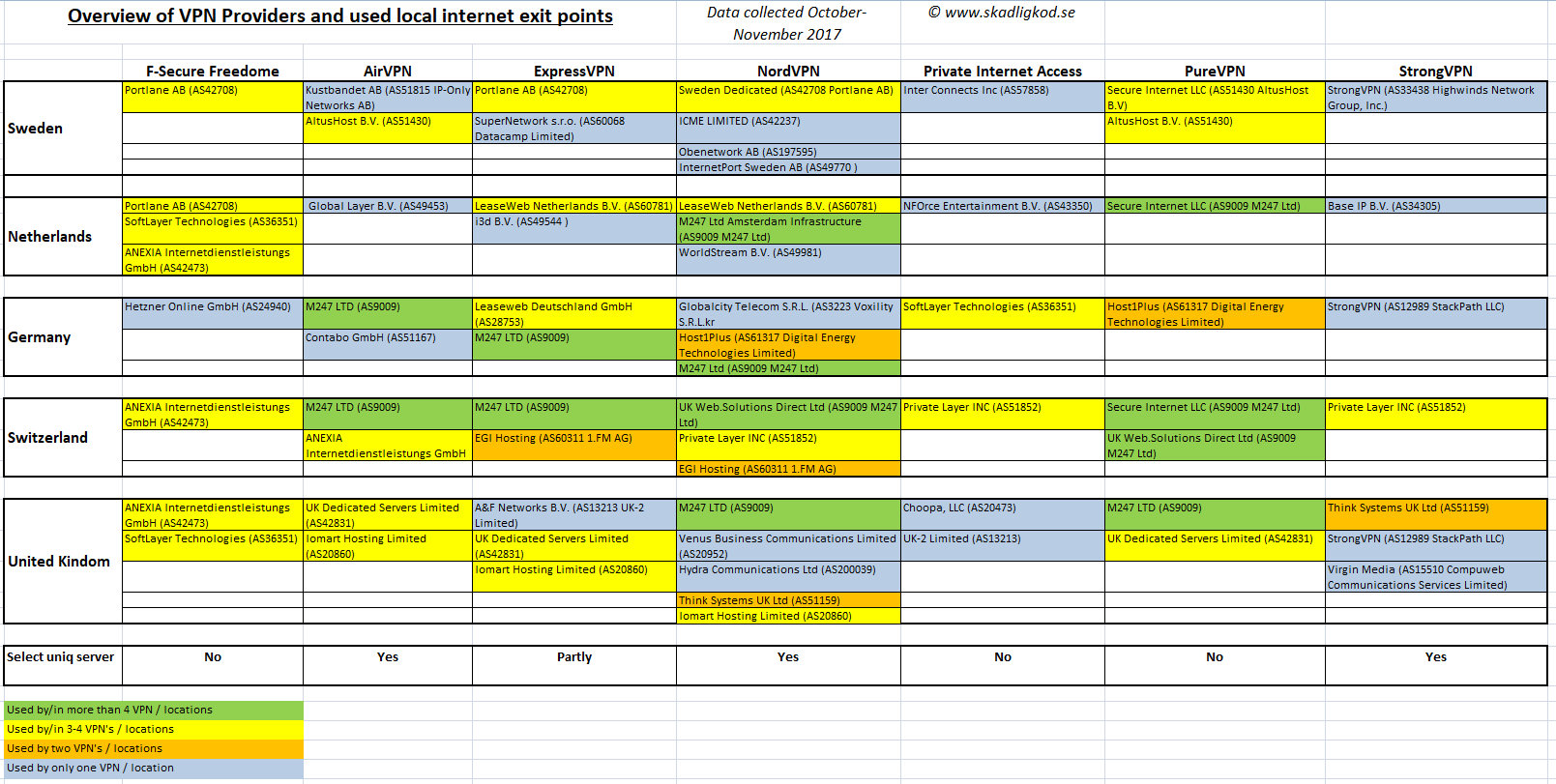
For this, I have made a comparison of internet exit points used by different VPN providers.
Comparing VPN’s to your local ISP – comparing internet exit points
To make a more objective review of VPN providers I simply checked which internet exit point (egress point) each VPN provider is using in a couple of countries. (during September – November 2017)
The following VPN providers were compared:
- F-Secure Freedome
- AirVPN
- ExpressVPN
- NordVPN
- Private Internet Access (PIA)
- PureVPN
- StrongVPN
Selected countries for the review:
- Sweden
- Netherlands
- Germany
- Switzerland
- United Kingdom
There are of course much more VPN providers and many more locations you can use depending on the VPN provider, but I had to stop somewhere.
Selection of unique server or just connecting to a random server in a country
Some VPN providers offer the selection of unique servers in each country, other providers just give the user the possibility to select one server in the country you want to connect to. In this case, the VPN provider automatically selects the server to connect to, based on the actual server load or other unknown criteria.
As mentioned at the beginning, each VPN provider has different jurisdictions, may differ in their logging policy and so on. Interestingly, many VPN providers use the same ISP’s or egress points in different countries as their competitors. Some differ and use more unique egress points.
Mapping of egress points used by VPN providers
The most commonly used egress point was owned by company called “M247 Ldt”. It was used by 4 out of 7 VPN providers in total. As well 4 out of 5 locations (missing / not present in Sweden).
Switzerland is the country with the fewest number of different egress points. In my review of VPN providers, none of them used an egress point that was unique. In the countries studied, all the VPN providers used servers that were also used by at least one other VPN provider.
As you see in the list, NordVPN provides the highest number of egress points in each country compared to other providers. In addition to this, NordVPN allows the user to individually choose the server to connect to, as well as automatically connect to any available server in a country. Hence the user has the freedom to choose.
Question of Trust
Do you trust M247 Ldt, Portlane, LeaseWeb, or for that matter, do you know enough to be able to make a decision?
Some providers give the user more control by offering the possibility to select a unique server to connect to, thus giving the user the possibility to “select” the local egress point. But the question is do you trust this egress point and by this the ISP connected to it?
The same applies for TOR, as an additional tool for privacy on the internet. As soon as you leave the exit node you have no protection. The difference is that TOR provides a strong protection of your identity, at least as seen from the exit node. With a VPN there will be a lot of traffic exiting over the VPN that potentially will identify the node using it such as OS update requests, browser feed updates, plugin updates etc. That traffic will to same degree identify the node in question if the traffic can be compared to know traffic from the node. Potentially clear text information, such as advertising, can directly identify the computer and therefore the user.
Choosing a VPN provider – Choosing an exit location
Based on the above findings, how should you choose your VPN provider?
Check each VPN provider’s homepage, they differ in price, number of servers and countries you can connect though. Some of them have additional features included such as an inbuilt web filter against malicious websites (F-Secure Freedome, NordVPN, PureVPN), or blocking trackers (F-Secure Freedome).
Some VPN providers such as NordVPN are offering double VPN, where the traffic is routed through two countries for increased anonymity. You may also want to use TOR in addition to your selected VPN provider to increase your privacy.
Use a VPN if you trust the egress infrastructure more than that of the network you are on. Examples could be if you are on a “free Wi-Fi”, a hotel network or in a country, such as USA, where internet providers have legal access to your traffic data. Don’t forget countries that block popular sites like China, Iran, Turkey and other countries. Using a VPN with an internet exit point different to the country you are in is highly recommended. Keep in mind that the usage of VPN services is illegal in some countries. Using a VPN there is on your own risk!
Finally, you must choose wisely and choose a VPN provider you can trust. But who can you trust and who not, if most VPN providers have overlapping egress points in different countries?
P.S. Thanks a lot @rndHashValue and @aajavis92 for your contribution to this article.
See also the recent User-Log case related to IPVanish.
A follow up on this article: Mapping of egress points used by VPN providers